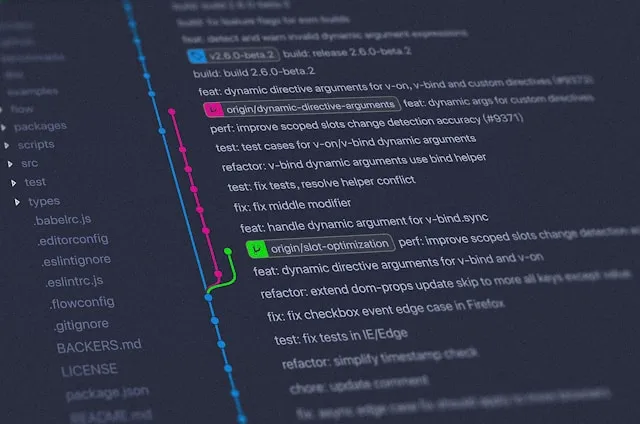
Flawed Git Promises Library on npm Leads to Command Injection Vulnerability
A promising Git library turns into a security nightmare when it harbors command injection vulnerabilities. Learn how to avoid these risks in your Node.js applications.
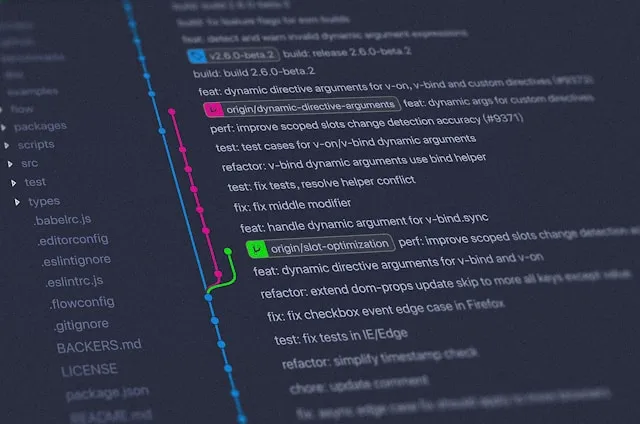
A promising Git library turns into a security nightmare when it harbors command injection vulnerabilities. Learn how to avoid these risks in your Node.js applications.
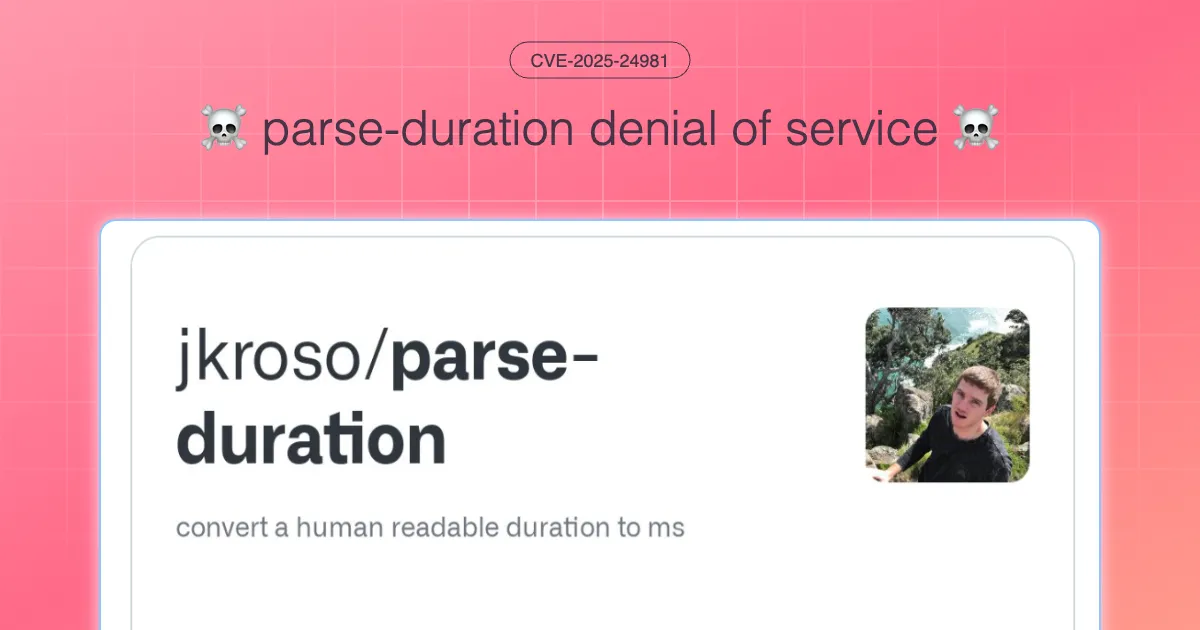
An in-depth analysis of two critical availability vulnerabilities in the parse-duration npm package, showing how regex patterns can lead to event loop delays and memory crashes in Node.js applications.

Are you using the Nuxt MDC library to render LLM generated content in your Nuxt.js apps? You want to read this article to understand how I came to find a Cross-site Scripting vulnerability identified today as CVE-2025-24981
Analyzing a vulnerability in safe-axios, an npm package designed to safeguard applications from SSRF attacks.

What if I told you that parsing URLs from user input, especially from Markdown content, can be a security risk? Here is how URL parsing logic an be bypassed and what you need to know to handle it in a secure way.

Learn about the npm `ignore-scripts` flag and how to use it to prevent the execution of arbitrary commands from malicious npm packages.